tips:suricata-eve-unixsocket
This is an old revision of the document!
Table of Contents
Suricata-EVE-Unixsocket
This article helps with providing guidelines for installing Suricata-Eve-Unixsocket app in Trisul Network Analytics.
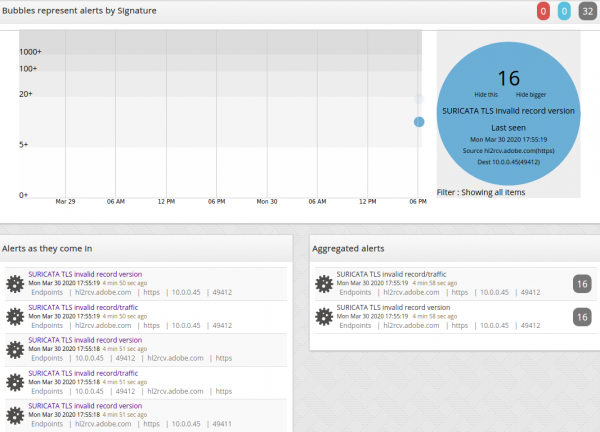
To create a threat signatures that will turn into a powerful frontline alert monitoring system for any enterprise.Usually Suricata show up as IDS alerts in Trisul.
Installation
1. Installing Suricata
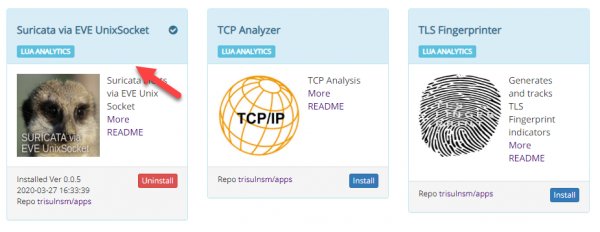
- You can install the app by logging in as admin and selecting Web Admin > Manage > Apps > Suricata via Eve Unixsocket.
- Please install Suricata by running the following command,
add-apt-repository ppa:oisf/suricata-stable sudo apt-get update apt-get install suricata
2. Installing Emerging Threat Rules
- You have to install the Emerging Threats Community which are a set of rules that trisul will listen to.
- Download and install Emerging Threats Open rules into /etc/suricata
#cd /etc/suricata #wget https://rules.emergingthreats.net/open/suricata-5.0.0/emerging.rules.tar.gz #tar xf emerging.rules.tar.gz
Please ensure that you run these commands in root
3. Enabling EVE output
- locate the 'Outputs' section in /etc/suricata/suricata.yaml enable EVE logging as shown below.
# Extensible Event Format (nicknamed EVE) event log in JSON format
- eve-log:
enabled: yes
filetype: unix_dgram #regular|
filename: suricata_eve.socket
The Filename is 'suricata_eve.socket' is the name of the Unix Datagram socket file that Trisul will listen to later.
- And, also disable the 'fast.log' in /etc/suricata/suricata.yaml as shown below.
outputs:
# a line based alerts log similar to Snort's fast.log
- fast:
enabled: no
filename: fast.log
append: yes
#filetype: regular # 'regular', 'unix_stream' or 'unix_dgram'
4. Starting Suricata
tips/suricata-eve-unixsocket.1598533883.txt.gz · Last modified: 2020/08/27 18:41 by navaneeth