This is an old revision of the document!
Table of Contents
How to analyze large PCAP dumps using the free TrisulNSM Docker
Quite a few of us have large packet capture dumps, but we dont quite know what do to with them. Some of the things we do are
- Wireshark : Just keep the PCAP dumps around, in case you need to you can carve small pieces of them and load them into Wireshark
- Argus or SiLK : Try to index them from a flow perspective. Argus or SiLK can do this.
- Bro : turn the PCAPs into bro logs, which record flows, dns, files, http request, and a number of other things
- Suricata / Snort : Run an IDS ruleset over the PCAPs.
- Security Onion : Play the PCAPs using TCP Replay and get all of the above.
- Moloch : Index the packets for fast recall
- TrisulNSM : Traffic metrics tool at its core, but does flows, index packets, extracts metadata, and other NSM tasks
We just released a free Trisul Docker Image that lets you do these easily in both online and pcap-file modes. Here is the blog post "Announcing TrisulNSM Docker"
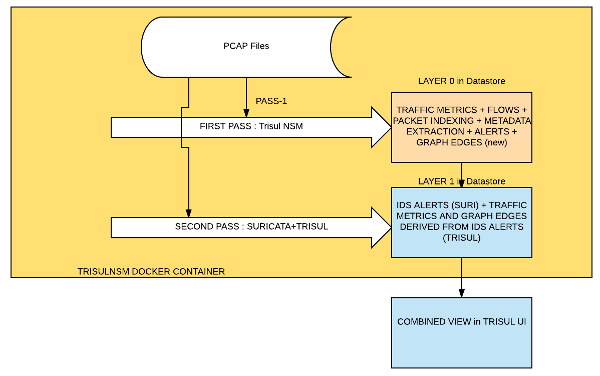
How it works : Two pass analysis
When you specify –pcap the Docker Image automatically runs two passes over the PCAP file.
- Pass 1 : Using Trisul, we collect deep traffic metrics, reconstruct and analyze flows, extract metadata, index and store packets. This goes to Layer 0 on the Trisul backend database.
- Pass 2 : Using Suricata + Trisul, we generate IDS alerts and convert those into metrics and graphs. Examples are vertices from a specific SIGID or Host. Top-k for hosts that are in attacker role, etc. This goes to Layer 1
The final result is a merger of Layer 0 + Layer 1. You can pivot from alerts to flows to TLS certificates down to packets.
Instructions : How to run the Docker image over PCAPs
First you need to create a root volume, say /opt/trisul6_root that will map into the Docker instance.
Then put the PCAP dump into the trisul root volume so that the docker image can read it.
mkdir /opt/trisul6_root cp /home/ec2-user/BSidesDE2017_PvJCTF.pcap /opt/trisul6_root
Run the free trisul6 docker image on the PCAP like so
docker run --name trisul1a --net=host \ -v /opt/trisul6_root:/trisulroot \ -d trisulnsm/trisul6 \ --pcap BSidesDE2017_PvJCTF.pcap
Now wait for the import to complete. Trisul is a streaming analytics platform, the time taken to complete the import is not proportional to the size of the PCAP, but to the duration of the PCAP. If your PCAP has two days traffic, then expect the import process to take up to 10-20 minutes. This also depends on the speed of the hard drive.
To check on progress you can do, when the import completes you will get a message asking you to login !
docker logs trisul1a -f
Of course you can also do the normal docker commands logging into the container docker exec -lt trisul1a /bin/bash Then use top or check the logs located under /usr/local/var/log/trisul-probe/
Single pass only
If you are not interested in IDS alerts that Suricata provides then you can do a single pass analysis with Trisul only. Use the –no-ids switch as shown below
docker run --name trisul1a --net=host \ -v /opt/trisul6_root:/trisulroot \ -d trisulnsm/trisul6 \ --pcap BSidesDE2017_PvJCTF.pcap \ --no-ids
Multiple imports
Once the import has been completed, the results are stored in a separate context. While logging in you select context you want to see. Login from http://ip-address:3000.
After completion you need to remove the instance and start a new one.
docker stop trisul1a docker rm trisul1a
Then you can import any number of files one after the other, they will be created in a separate context each time, so you can keep the data sets separate.
Free image
The docker image includes a Free License of Trisul that allows PCAPs of a maximum of 3 days. This should suffice for most people.